Malicious npm Turn Developer Tools Into Attack Infrastructure
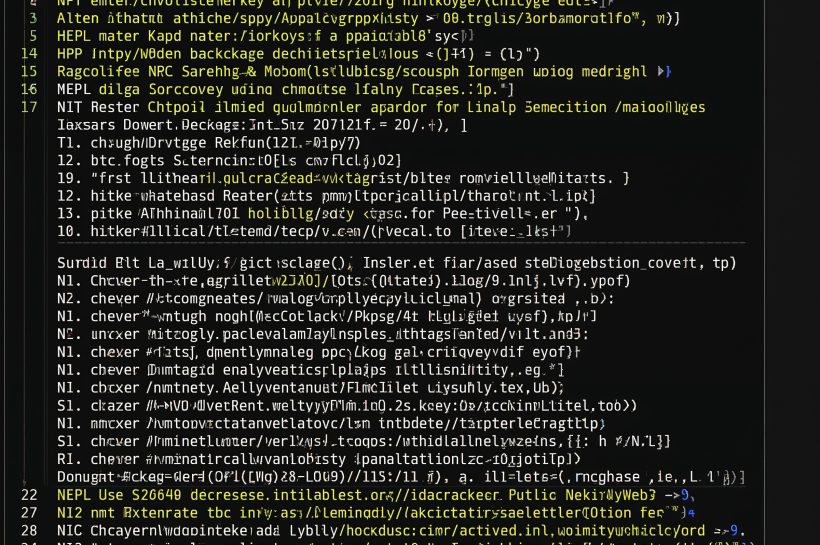
Malicious npm packages are being used as hidden attack infrastructure, abusing the open-source supply chain to distribute malware, evade detection, and compromise developer environments.
Malicious npm packages are being used as hidden attack infrastructure, abusing the open-source supply chain to distribute malware, evade detection, and compromise developer environments.
The threat landscape that shaped cybersecurity in 2025 reveals how identity abuse, ransomware evolution, and supply chain risks forced organizations to rethink defense strategies.

Multiple vulnerabilities in TeamViewer DEX expose risks in enterprise endpoint monitoring platforms, raising concerns about unauthorized access, telemetry abuse, and internal reconnaissance within corporate environments.
A security incident involving the Trust Wallet Chrome extension shows how attackers can abuse browser extension architecture to compromise cryptocurrency wallets and silently expose user funds.

A China-linked cyber espionage malware campaign demonstrates how attackers abuse DNS traffic to maintain stealthy, long-term command-and-control access.

Parrot OS 7.0 delivers a stability-focused update for security professionals, refining penetration testing tools, system performance, and privacy features while maintaining a practical, research-driven Linux environment.
Recent cyber threats highlight a sharp rise in stealth malware loaders and AI-assisted attack techniques, signaling a shift toward quieter, more adaptive initial access strategies that challenge traditional detection models.

Growing interest in a Trump-aligned tech workforce initiative highlights how AI job seekers are responding to rising demand for artificial intelligence skills across the U.S. technology sector.

Microsoft has rolled out hardware-accelerated BitLocker support for Windows 11, delivering faster encryption, lower CPU overhead, and stronger device protection. This update significantly improves enterprise deployment and endpoint security strategies.
A phishing vulnerability in vLex’s Vincent.ai exposed lawyers and law firms to AI-driven cyberattacks. Attackers manipulated the legal research tool to embed malicious links into AI-generated responses, creating a new avenue for targeted phishing in the legal sector.